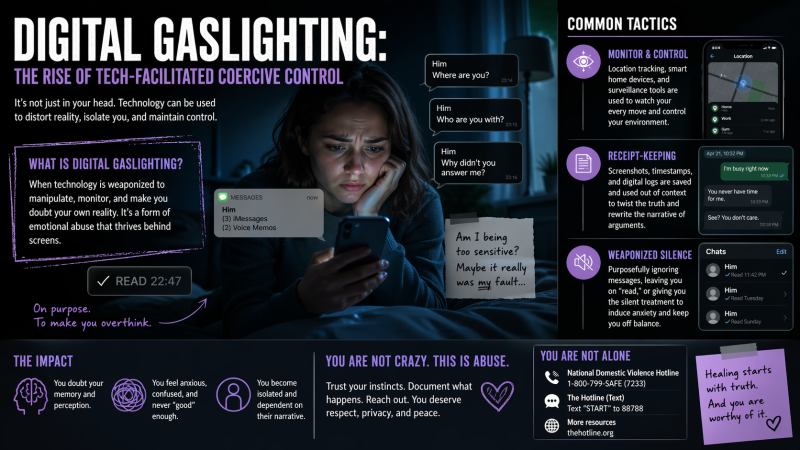
Weaponised Silence and Message Manipulation
A common tactic is digital silent treatment: reading texts or emails without replying. Leaving a partner “on read” can trigger severe anxiety and self-doubt, much like the traditional silent treatment in abuse. As health experts explain, when someone uses silence to punish or control (“I notice you’re not responding”), it becomes emotional abuse. In practice, abusers mix ghosting with other tricks – they may acknowledge a partner’s text but refuse to respond (creating panic) or deliberately respond too late. Over time this breaks down confidence: the victim feels “not good enough” or overly needy when their partner ignores them. It’s a subtle form of “passive aggression” that coerces obedience without direct confrontation.
Example: A controlling partner might see a message, wait hours to read it, then suddenly reply “sorry, I was busy” whenever convenient. The uncertainty – “Will they ever text back?” – creates constant stress. As one survivor notes, “Immediately all the reasons why a person wouldn’t respond become so loud in my head”. Specialists warn this is a strategy: a deliberate anxiety-building technique that makes victims hyper-vigilant and submissive.
Digital Records and “Receipt-Keeping”
Another tactic is manipulating digital evidence. Abusers screenshot or record interactions to twist later – a kind of “receipt-keeping” to rewrite history. For example, an abuser may secretly record a victim during an argument and later edit clips to look as if the victim were the aggressor. In court, this can flip the narrative (a pattern called “DARVO”: deny, attack, reverse victim and offender). As psychologist Lisa Fontes observes, “domestic abusers rely on recordings to claim that their victims are actually the predominant aggressors… This is a form of gaslighting”. Victims often end up defending themselves against the fraudulent evidence the abuser manufactured.
In the digital realm, abusers also alter or delete electronic communications. They might deny sending certain texts or change chat screenshots to make the victim doubt what really happened. For example, a message that once said “I love you” might be replaced with silence, and the abuser then insists “you never said that”. This sudden disappearance of evidence causes victims to question their memory and sanity. Justice advocates note this tactic: if a victim “does not document evidence” (screenshots of flickering lights or doorbell chimes caused by a remote device), the abuser can gaslight them by saying it was imagined. In short, digital logs become weapons.
Surveillance: Tracking Apps and Smart-Home Devices
Technology also allows 24/7 surveillance. GPS trackers and phone apps can silently report a partner’s every move. Stalkerware apps (often disguised on phones) send constant location updates. Social media features like live location sharing or “check-ins” are abused to ambush or threaten. Experts list the signs: the victim feels “found wherever they go,” odd Bluetooth devices appear nearby, battery life suddenly plummets – all clues of covert tracking.
Beyond phones, smart home devices become tools of control. Abusers who set up a home’s technology can later “haunt” the survivor with it. For instance, a partner might remotely access a smart thermostat or lights to make a home unbearably hot or cold; they might turn cameras or doorbells on/off to spy or intimidate. One chilling Lawfare scenario describes a manipulator who, after eviction, gleefully blares music, flickers lights and toggles temperatures via their ex’s apps – then threatens further escalation if the victim doesn’t comply. In real cases, victims report receiving notifications like “Your location was pinged” from a partner’s car app, or finding the kitchen camera on their fridge turned towards them – a constant invasion of privacy. Abusers can even use connected cars: remote-engine-disabling or location tracking in vehicles has stranded survivors on highways when they flee.
Wearables and the “Internet of Lies”: Fitness trackers and smartwatches are exploited too. Abusers monitor heart rate or sleep patterns via apps, then use spikes in heartbeat during arguments as “proof” the victim is lying or lying to them. Voice assistants (Alexa, Google Home) are another vulnerability: a victim whispering about seeking help can be overheard and later twisted into accusations of “lying” about seeking therapy. In one example, victims unplug speakers in fear, only to have the abuser accuse them of hiding something. These stealthy invasions mirror classic gaslighting: they manipulate environment so the survivor feels paranoid and disoriented.
Isolation and Social Control
Tech abuse also isolates victims. Abusers may demand passwords, lock victims out of social media or banking accounts, and force them to delete friends or contacts. This cuts off support networks. For example, forcing a partner to unfollow close friends online, or controlling who they can message, prevents them reaching out when in danger. Fake online personas (“sock-puppet” accounts) can be created to spy on the victim or feed them false accusations, further breaking their trust in reality. Netsafe (NZ) highlights warning signs: if someone seems to know private details you haven’t shared, or if you suddenly have “frequent password resets you did not initiate” and messages vanish mysteriously, it likely means they’ve got remote access. Posting embarrassing photos or rumors online is also used to turn friends against the victim.
Together, these tactics–tracking, gaslighting, exclusion–form a web of digital coercion. Each move is designed to make the victim feel powerless and alone. A survivor under tech abuse may find themselves constantly “modifying their behaviour” to avoid setting off alarms on home devices, or checking over their shoulder if their movements or words were secretly recorded. In short, technology extends the “power and control” wheel into the digital sphere.
The Psychological Toll and Emerging Research
The impact is severe. Victims often report chronic anxiety, depression and a feeling of being “gaslit” into doubting their own judgement. Because the abuse is hidden behind screens, it’s notoriously hard for outsiders to see. Law enforcement and even courts may misunderstand it: as one study notes, officers sometimes dismiss non-physical stalking through devices as low-risk because it’s “not visible”. Yet studies show tech-enabled stalking correlates with high danger: in fact, 100% of survivors report that digital harassment escalates around separation, just as with physical stalking.
Research is now catching up. A flurry of recent studies and reports underline that “tech abuse” is not a fringe issue. For example, a 2026 CHI conference study found ChatGPT-like AIs can be misused by abusers to craft manipulative messages or plan stalking, noting these tools can “facilitate harassment, intimidation, gaslighting, monitoring, surveillance, and other coercive control tactics”. Another comprehensive review confirms “digital technologies can play damaging roles in facilitating coercive control,” with abusers learning online how to exploit every new gadget. Even law journals warn of a “Domestic Violence Dystopia” as IoT devices proliferate. These analyses validate what survivors have long known: abuse can travel through every app and appliance.
Current Thinking: Modern psychologists emphasize that digital gaslighting is just old abuse in new clothes. All the classic gaslighting moves (denial, diversion, trivialisation) now happen with a tech twist. For instance, an abuser might pretend not to receive texts (“your phone must be broken”) or shuffle security cameras after the fact to claim the victim was imagining disturbances. Experts therefore advise validating victims’ experiences even when evidence is “invisible.” Key signs include: unexpected device behaviours (messages read without response, apps turning on, rogue logins), sudden tech malfunctions, or arguments that hinge on confusing “proof” (screenshots or recordings) that only the abuser controls.
Protecting Yourself: Evidence and Resources
If you suspect digital abuse, focus on safety and documentation. Save evidence on a device the abuser cannot access. Screenshot threatening texts, emails, app activity or smart-device logs, and store them in a secure folder or cloud account. Do not delete abusive messages; experts warn that deleting evidence can hurt you later – instead, back them up and reach out to a support worker first. Keeping a dated log of incidents (time, date, what happened) is also crucial. The infographic above (from a UK domestic abuse service) outlines these steps in detail, such as photographing signs of abuse on devices and forwarding evidence to a trusted email.
Device Safety Tips: Use a “clean” or alternate phone/computer for critical activities (sending yourself evidence, contacting hotlines). Log out of apps and reset passwords on devices you keep (if safe to do so) to prevent the abuser from spying. Check for unfamiliar apps or paired devices (e.g. tracking software). Consider changing account credentials on a secure Wi-Fi or friend’s device. Experts also recommend installing antivirus alerts for stalkerware and reviewing account-access logs (most email/social sites allow you to see recent logins). Remember: your safety comes first; only make tech changes if you won’t alert the abuser to your actions.
Reach Out for Help: Digital abuse is increasingly recognised as a form of domestic violence, and specialized help is available. You are not alone. Organisations like NIDAS (UK), Netsafe (NZ) and various domestic violence hotlines offer confidential advice on tech safety. Many have online guidance or helplines specifically for digital abuse. If immediate danger arises (e.g. location stalking or threats), call emergency services. Otherwise, speaking to a specialist support worker can guide you on safe steps, such as legally protecting evidence or disentangling devices from an abuser.
Seek Support: Talking to friends, family or counselors about odd tech incidents can help confirm you’re not overreacting. A trusted person might notice patterns you haven’t, or help validate your memories. Counselling (online or off) is also encouraged: these services understand that trauma can make victims blame themselves. You deserve belief and support.
Prevention: Going forward, keep communication lines open with someone you trust. Set up backup ways of contacting help (e.g. memorised numbers, hidden email) in case apps are compromised. Use strong, unique passwords and consider multi-factor authentication (MFA) that ties to you alone. For any new smart devices (speakers, cameras), review privacy settings – disable unnecessary data sharing and regularly audit who has account access. Importantly, no one should feel guilty for owning tech; instead, demand that tech developers and lawmakers make devices safer by default and enforce accountability when they are abused.
Understanding digital gaslighting as a real and serious abuse strategy is the first step to fighting it. By recognizing these modern tactics – silent treatment via text, covert tracking, evidence manipulation – victims and allies can reclaim control. If anything here resonates with your experience, reach out. Help is out there, and with the right support and tools, the digital playground can become a place of empowerment rather than fear.
Sources: Research and guidance from domestic abuse experts and recent studies on tech-facilitated abuse provide the basis for this overview, as do resources from UK and NZ advocacy organisations.